

Every organization has a different set of security skills and objectives, whether protecting workstations, locking down servers, or integrating with your security stack. Only Carbon Black provides you with the most choice in next-generation endpoint security, so we can cover you no matter what your situation is.
Carbon Black has built the world’s most advanced security system, providing streaming prevention, detection, and response, delivered from the cloud. With complete visibility into known and unknown threats, plus up-to-the-minute protection based on worldwide trends, Carbon Black provides the strongest protection from the latest outbreaks of ransomware, malware, and non-malware attacks.
Carbon Black easily integrates with your entire security stack, resulting in the best possible protection by enabling your security products to work together. Through our extensive partner ecosystem, we provide out-of-the-box integrations for more than 70 leading security products from vendors such as IBM, Splunk, VMware, and Palo Alto Networks. Additionally, our open APIs enable customers to build deep integrations with any security product or enterprise system.
Carbon Black's products are certified to replace antivirus, protect sensitive information, and meet compliance requirements. This is just one more reason why their solutions have earned the trust of leading analysts and industry associations.
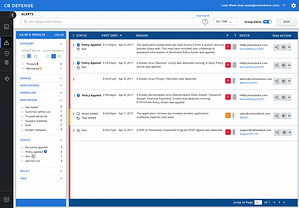
Cb Defense
Next-generation antivirus + EDR in one cloud-delivered platform that stops malware and non-malware attacks

Stop the MOST attacks
53% of breaches do not use malware. Streaming prevention goes beyond machine learning AV to stop all types of attacks before they compromise your system.
-
Stop malware, ransomware, and non-malware attacks
-
Prevent attacks automatically, online and offline
-
Block emerging, never-before-seen attacks that other solutions miss
See how Streaming Prevention Works
See EVERY Threat
97% of organizations will be targeted by a non-malware attack. Our market-leading detection and response capabilities reveal threat activity in real time, so you can respond immediately to any type of attack.
-
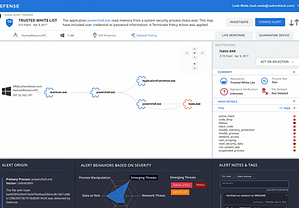
Continuous and centralized recording provides complete visibility into the attack
-
Quickly visualize the attack chain to see exactly what attackers are trying to do
-
Automated threat hunting, powered by the cloud, keeps you one step ahead of every attack
Compromise NOTHING
1 in 3 organizations will be targeted by a non-malware attack in the next 90 days. Quickly take back control with a single agent, a simple cloud console, and virtually no impact to end users.
-
Deploy in 15 minutes or less, with less than 1% CPU and disk space per endpoint
-
Lightweight agent won’t impact performance, keeping users happy and productive
-
Effective security that balances total visibility, automated prevention, and minimal user impact
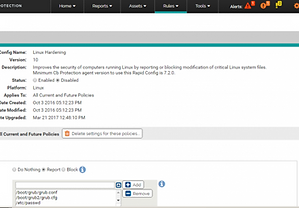
Cb Protection
The most trusted way to lock down servers and critical systems with 100% efficacy with the the only Unbreakable Application Control Solution on the market.
BEST possible protection
Cb Protection was the only solution to stop 100% of attacks in NSS Labs' Advanced Endpoint Protection (AEP) test.
-
Lock down systems to stop malware, ransomware, zero-day, and non-malware attacks
-
Built-in file-integrity monitoring, device control, and memory protection to block unauthorized change
-
Harden new and legacy systems, with broad support for embedded, virtual, and physical OSes
CONTINUOUS Compliance
The cost of compliance is outpacing any other spend in IT. Make regulatory and policy compliance easier and less costly with Cb Protection.
-
Continuous and centralized recording provides complete visibility into the attack
-
Quickly visualize the attack chain to see exactly what attackers are trying to do
-
Automated threat hunting, powered by the cloud, keeps you one step ahead of every attack
HIGH Performance, LOW Touch
Cb Protection is the most proven and scalable application control solution on the market. A single admin can manage over 10,000 systems, giving security teams total control with little ongoing effort.
-
Out-of-the-box templates based on industry best practices keep management overhead low
-
Cloud-based reputation and detonation helps you make fast decisions about which software to trust
-
Automatically trust software deployed by IT to keep administration easy and achieve fast time-to-value
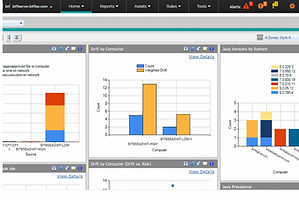
Cb Response
Market-Leading Incident Response & Threat Hunting. Detect attacks in progress and respond immediately. Highly scalable, real-time EDR with unparalleled visibility for top security operations centres and incident response teams.

UNLIMITED Scale
A large enterprise can have hundreds of thousands of endpoints, but an attacker only needs to breach one. You need a solution that scales with your entire organization to hunt and stop the advanced attacker.
-
Unlimited data retention for investigating long-term attacks with extreme dwell time
-
Sophisticated data analytics and visualization tools built for big data at scale
-
Lowest TCO with no impact on the end user and minimal resource usage
Learn How to Reduce the Costs of Incident Response

COMPLETE Visibility
Investigations that typically take 78 hours can be completed in 15 minutes. Cb Response captures more information about more events than any other solution, giving incident responders the most complete picture possible.
-
Full access to the complete data record of every endpoint, even if it is offline
-
See what happened at every stage of the attack with easy-to-follow attack chain visualizations
-
Uncover root cause in minutes to quickly address gaps in your defences

PROACTIVE Threat Hunting
The average breach takes 150 days to discover—unless your team is proactively hunting threats, detecting attackers, and shutting them down with Cb Response.
-
Fast search, zoom, and visualization of process trees and timelines to pinpoint threats in seconds
-
Consolidate threat intelligence for your environment to automatically detect suspicious behaviour
-
Correlate network, endpoint, and SIEM data through open APIs and out-of-the-box integrations

REAL-Time Response
An attacker can compromise your environment in an hour or less. Cb Response gives you the power to respond and remediate in real time, stopping active attacks and repairing damage quickly.
-
Isolate infected systems to prevent lateral movement and remove malicious files
-
Secure shell access to any endpoint through "Live Response"
-
Automatically collect and store detailed forensic data for post-incident investigation



